API Keys
API keys allow you to interact with the YipYap API from scripts, CI/CD pipelines, and external integrations.
Setup Guide
Section titled “Setup Guide”- Navigate to Settings > API Keys.
- Click New API Key.
- Enter a descriptive name that identifies the integration (e.g. “CI Pipeline”, “Terraform Provider”).
- Select only the scopes this key needs. Follow the principle of least privilege.
- Click Create.
- Copy the key immediately. It is displayed only once and cannot be retrieved later.
- Store the key in a secrets manager or environment variable. Never commit it to version control.
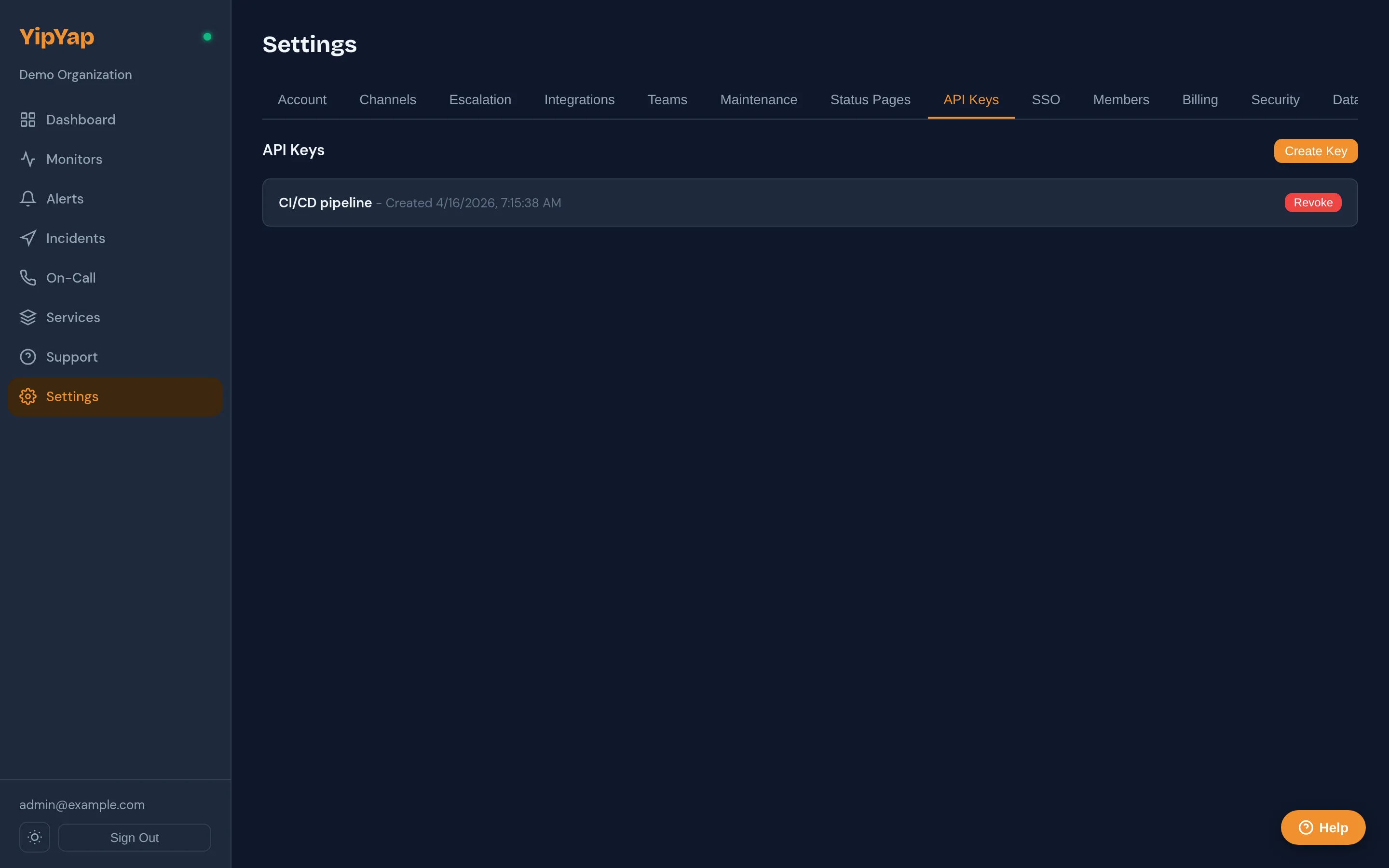
Creating an API Key
Section titled “Creating an API Key”- Navigate to Settings > API Keys.
- Click New API Key.
- Enter a descriptive name (e.g. “CI Pipeline”, “Prometheus Integration”).
- Select the scopes the key needs.
- Click Create.
The key is displayed once. Copy it and store it securely. You cannot retrieve the key after closing the dialog.
Scopes
Section titled “Scopes”| Scope | Description |
|---|---|
monitors | Read, create, update, and delete monitors. |
alerts | Read, acknowledge, and resolve alerts. |
escalation_policies | Manage escalation policies. |
notification_channels | Manage notification channels. |
maintenance_windows | Manage maintenance windows. |
Assign the minimum scopes required for each integration. This follows the principle of least privilege.
Using the API Key
Section titled “Using the API Key”Include the key in the Authorization header of your API requests:
curl -H "Authorization: Bearer yy_live_abc123..." \ https://console.yipyap.run/api/v1/monitorsKey Management
Section titled “Key Management”- Rotate: Create a new key, update your integrations, then delete the old key.
- Revoke: Click the delete button next to any key to revoke it immediately. All requests using that key will fail.
- Audit: The API Keys page shows when each key was last used.
Rate Limits
Section titled “Rate Limits”API requests are rate-limited to 300 requests per minute per key. If you exceed this limit, the API returns 429 Too Many Requests. Implement exponential backoff in your client to handle rate limits gracefully.
Security
Section titled “Security”- Never commit API keys to version control.
- Use environment variables or a secrets manager to store keys.
- Rotate keys periodically and after any suspected compromise.